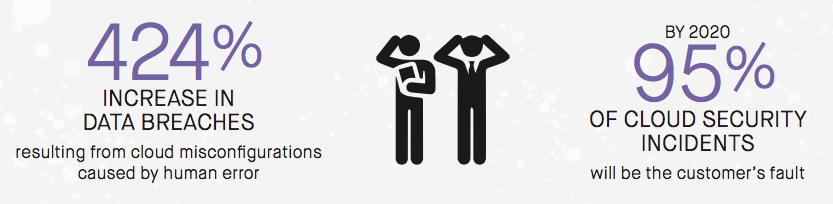
Infrastructure misconfiguration has become increasingly likely as companies migrate more of their workloads to the cloud. Being on cloud means being dynamic and agile, and the security solutions used to protect data centers are not as effective in the cloud. Properly configuring a cloud resource requires new set of skills and an understanding of how to manage cloud resources. In addition, traditional security tools will not be as effective because they are focused at the operating system and application level. Another culprit will be the human error on the customer’s end. Gartner predicts that by 2020, 95% of all cloud security incidents will be the customer’s fault.
A cloud misconfiguration can occur anywhere in your infrastructure. Time delay is your worst enemy when it comes to misconfigurations. The longer it takes to find and fix misconfigurations means heightened security risks. If you are not examining your entire cloud infrastructure stack, including your network, storage, and numerous other cloud services for misconfigurations, you are leaving the security door wide open.
Download our data sheet on why CISOs should care about Mean Time to Remediation for cloud misconfigurations here.
Look for Part 2 of this post next week.
